Table of Contents
EECS Linux Systems And Duo Authentication
The University of Tennessee's chosen two-factor authentication system is Cisco System's Duo. Virtually all university services require a password and either a Duo push notification or a Duo passcode for authentication. Two-factor (2FA) authentication is an important tool to help mitigate the threat of compromised user accounts. Beginning in the Spring semester 2022, EECS IT will add two-factor authentication to many departmental IT services.
From UT's two factor (2FA) authentication website:
2FA boosts protection of your account from hackers. We are all used to having one layer of security — our password — to protect our accounts. With 2FA, if the hackers have your password, they will still need your phone or passcode to get into your account.
When using 2FA, you’ll be required to use two different sources (factors) to verify your identity:
- Something you know – your username and password, and
- Something you have – a phone or passcode, to authenticate and gain access to an account. For example, this may be a smartphone or tablet using an app or a hardware token device.
This document will refer to the process of password/two-factor Duo authentication simply as “Duo authentication”. However, a password is always required as well.
SSH Duo Authentication Rollout
Secure Shell (SSH) authentication to EECS Linux systems will require Duo authentication, either directly or by use of the UT VPN. EECS IT will begin rolling out Duo authentication for supported Linux systems during the Spring semester 2022. This deployment will happen in four phases:
- Phase II: EECS Red Hat Enterprise Linux 7 virtual lab systems such as the VLSI lab.
Timeline: Early Spring semester, 2022 - Phase III: EECS Red Hat Enterprise Linux 7 individual desktop systems.
Timeline: Spring 2022 - Phase IV: EECS IT-supported Linux research servers:
Timeline: TBD
Secure Shell (SSH) and Duo
Where will DUO be required?
All SSH connections will prompt for Duo authentication with the following exceptions:
- Connections from trusted EECS-IT supported Linux systems. E.g. connections from one Hydra lab system to another will not require Duo authentication.
- Connections from the UT Ivanti Secure Access VPN. Since the VPN already requires Duo authentication, no additional two-factor is required.
Public Key Authentication
Public key authentication (aka SSH keys authentication, Pubkey authentication) bypasses the normal password and Duo authentication mechanism. Thus, public key authentication will be restricted to the same set of exceptions that are listed above, i.e. public key authentication will continue to work when logging on from a trusted system or the VPN.
Public Key Authentication From Home
To make this clear, if you are currently using a public/private key pair to log into EECS Linux systems from home, you will need to connect to UT's VPN to ssh into EECS Linux systems.SSH with Duo
Logging in to a system with Duo authentication enabled is not much different from a regular SSH password-based login. After authentication with their password, a user is presented with a Duo prompt where they can choose to enter a passcode (displayed in the Duo mobile app) or, if they have a mobile phone registered with Duo, receive a push notification or SMS.
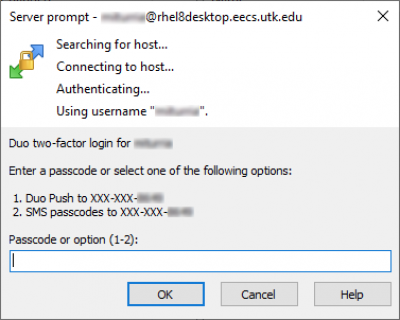
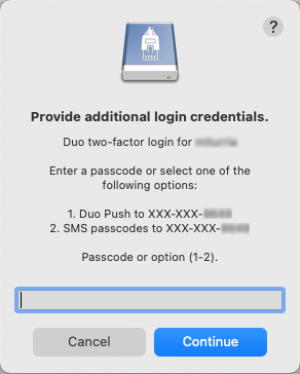
Text-based SSH
Shell/text-based SSH clients (OpenSSH in MacOS, Windows (both native and WSL), Linux, etc.) will see a prompt like this:
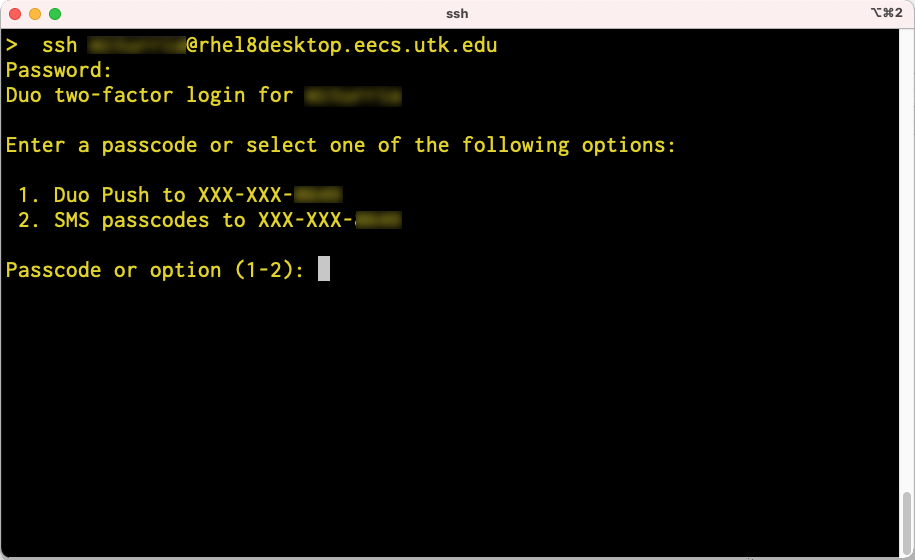
Simply enter a passcode or select one of the two options to continue.
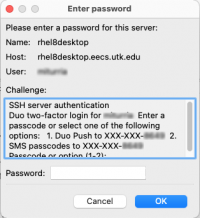
GUI SSH
GUI SSH/SFTP clients must support the keyboard-interactive authentication method to be able to use Duo authentication. Verified working clients include:
Windows
MacOS
- FileZilla - see below
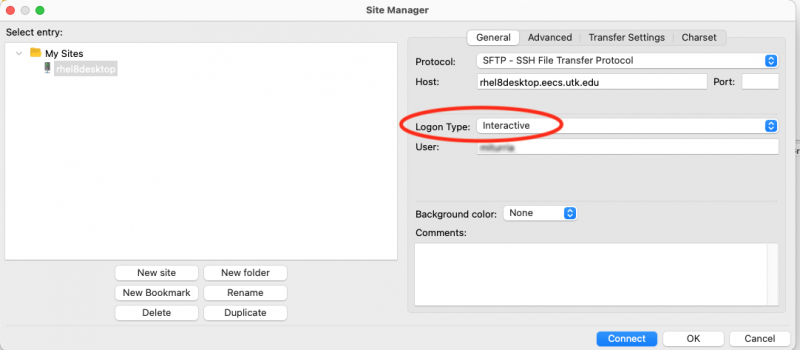
Manually Setting Authentication Method
Some SSH/SFTP clients, e.g. FileZilla, may require the authentication method to be manually selected. For Duo authentication this should be “keyboard-interactive” or “interactive”. If you favorite client no longer works, look for this setting. It may be called Authentication Method, Logon Method, Logon Type, or something similar.
Example: Manually setting the authentication method in FileZilla:
Other Login Types and Duo
Remote Logins
In addition to secure shell, some EECS systems support other login types, for example RealVNC connectivity. EECS IT will begin to add Duo authentication to these services as well. This will happen either by adding Duo directly to those services that support it or by placing access to the service behind UT's VPN. More information will be added to this page as changes are made.
Local Logins
EECS IT currently has no plans to add Duo authentication to most local logins to EECS systems. (A local login, sometimes known as a “console” login, means typing your user name and password directly into the system's keyboard and using the system's screen.) Exceptions to this include systems that require extra security as determined by the system owner or by a system security plan. If you wish to add Duo authentication to your EECS desktop, please contact the EECS IT Staff for assistance.